In an era where digital security is paramount, Windows 10 stands as a fortress against potential threats, offering users robust tools to safeguard their sensitive information. Among these tools, BitLocker Encryption takes center stage, providing a formidable defense mechanism against unauthorized access and data breaches. This extensive guide aims to unravel the complexities of Windows 10 BitLocker Encryption, exploring its functionalities, implementation, customization options, and the crucial role it plays in ensuring the confidentiality and integrity of user data.
Understanding BitLocker Encryption
BitLocker Encryption is a built-in feature in Windows 10 that empowers users to encrypt their drives and protect the data stored on them. Whether you’re using a desktop, laptop, or external storage device, BitLocker acts as a shield, scrambling the contents of the drive in such a way that only authorized users with the correct credentials can access the data.
- Drive Encryption vs. File Encryption: A Fundamental Distinction
BitLocker operates at the drive level, encrypting the entire contents of a drive, including the operating system, system files, and user data. This distinguishes it from file-level encryption, as it ensures comprehensive protection for all data on the encrypted drive, irrespective of the file type.
- Trusted Platform Module (TPM): Enhancing Security Foundations
BitLocker relies on the Trusted Platform Module (TPM) to fortify its encryption capabilities. TPM is a hardware-based security feature that provides a secure environment for storing cryptographic keys. By leveraging TPM, BitLocker establishes a foundation for secure encryption, ensuring that encryption keys are protected from potential tampering or unauthorized access.
- BitLocker in Windows 10 Editions: An Inclusive Security Approach
BitLocker is available across various editions of Windows 10, ensuring that users with different versions of the operating system can benefit from its encryption capabilities. While BitLocker is present in Windows 10 Home, it offers more advanced features and management options in Windows 10 Pro, Enterprise, and Education editions.
Implementation of BitLocker Encryption
- Activating BitLocker: A Step-by-Step Encryption Journey
Activating BitLocker is a straightforward process that involves a series of steps to ensure a seamless encryption experience. Users can initiate BitLocker through the Control Panel or by right-clicking on the drive they wish to encrypt in File Explorer. The step-by-step wizard guides users through the necessary configurations, allowing them to choose their preferred encryption method and settings.
- Choosing Encryption Methods: Balancing Security and Convenience
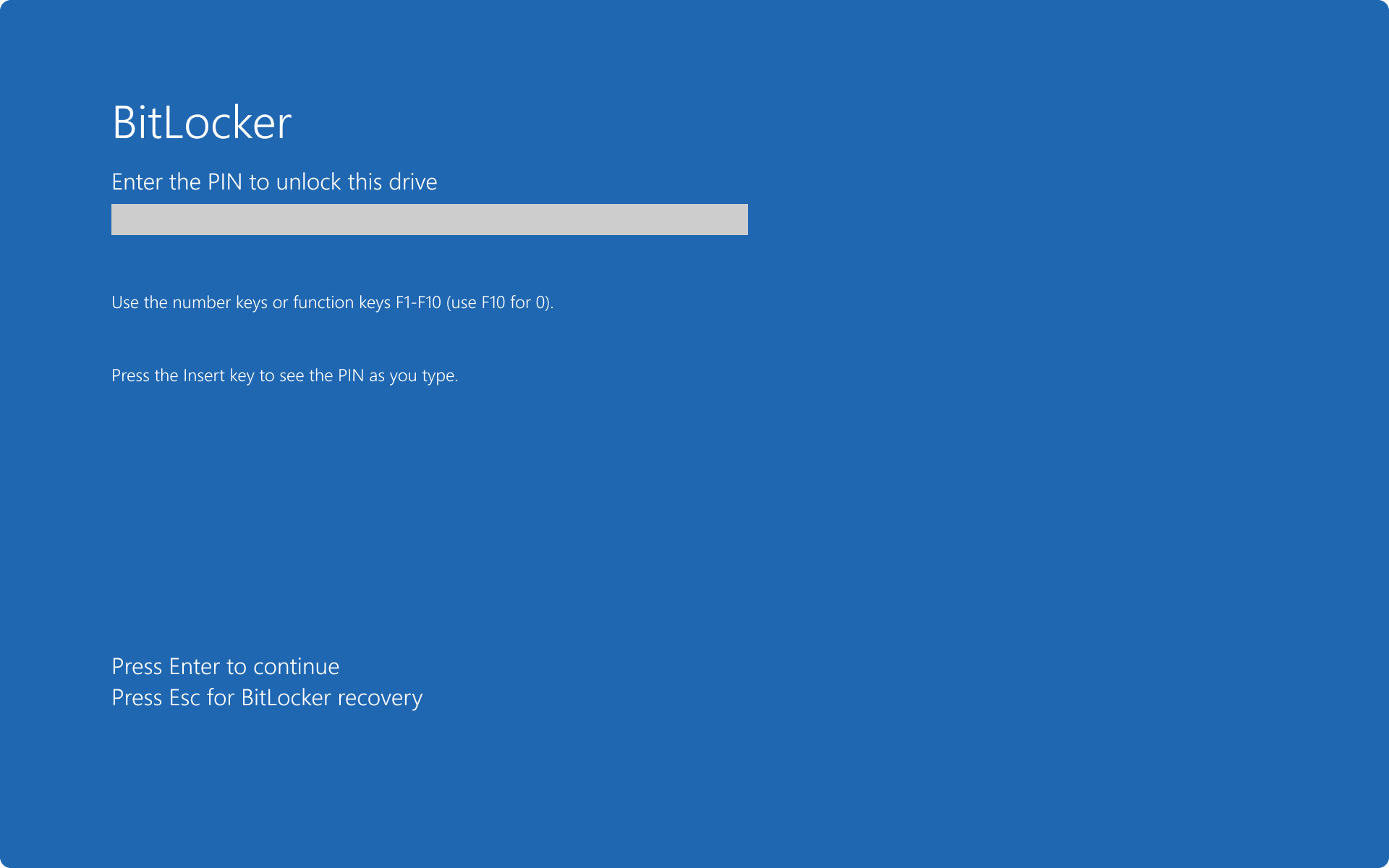
BitLocker provides users with multiple encryption methods to choose from, each offering a balance between security and convenience. Users can opt for the standard BitLocker encryption, which requires a password or PIN at startup, or they can leverage advanced options such as using a USB key for authentication or incorporating TPM-only protection.
- Recovery Key and Password: Safeguarding Access in Unforeseen Circumstances
BitLocker prompts users to generate a recovery key during the encryption setup process. This recovery key serves as a critical safeguard in case users forget their passwords or encounter issues accessing their encrypted drives. Users can choose to save the recovery key to their Microsoft account, print it, or store it in a secure location.
Customization Options for Tailored Security
- Group Policy and BitLocker: Centralized Control for Enterprises
For enterprises managing multiple devices, Group Policy provides a centralized approach to configuring and managing BitLocker settings. Administrators can enforce encryption policies, set recovery options, and ensure consistent security standards across all devices within the network.
- BitLocker To Go: Extending Encryption to Removable Drives
BitLocker To Go extends the encryption capabilities of BitLocker to removable drives such as USB flash drives and external hard disks. Users can enable BitLocker protection for these drives, ensuring that data remains encrypted even when transferred between different devices.
- Network Unlock: Streamlining Boot Processes in Enterprise Environments
In enterprise environments with multiple computers connected to a network, BitLocker’s Network Unlock feature streamlines the boot process. By leveraging network authentication, BitLocker ensures that devices connected to the corporate network can automatically unlock encrypted drives during startup, reducing user intervention and enhancing efficiency.
- Pre-boot Recovery Message: Facilitating User Guidance
BitLocker allows users to customize pre-boot recovery messages, providing essential guidance in case of password prompts or recovery key requests. This feature enhances user awareness and ensures that individuals interacting with encrypted devices understand the necessary steps for accessing their data.
- Smart Card Authentication: Strengthening Identity Verification
In environments where heightened security measures are required, BitLocker supports Smart Card authentication. Users can configure BitLocker to use Smart Cards as an additional layer of identity verification, ensuring that only authorized individuals with the corresponding Smart Cards can access encrypted drives.
Best Practices for Managing BitLocker Encryption
- Regular Backups: A Precautionary Measure for Data Resilience
While BitLocker enhances data security, it’s crucial for users to implement regular backups of their data. Backups provide a safety net in case of unforeseen events, ensuring that users can recover their data even if issues arise with the encrypted drive or the BitLocker encryption process.
- Regular Password Updates: Enhancing Security Hygiene
To bolster security hygiene, users are encouraged to update their BitLocker passwords periodically. Regular password changes reduce the risk of unauthorized access and align with best practices for maintaining robust data security.
- Device Decommissioning: Safeguarding Data Beyond Usage
When decommissioning devices that have been protected by BitLocker, it’s imperative to follow secure data disposal practices. This may involve decrypting the drive before device disposal, ensuring that sensitive data is rendered inaccessible to any potential unauthorized users.
Advanced Security Considerations
- BitLocker and Secure Boot: A Synergistic Security Approach
Secure Boot is a complementary security feature that works hand-in-hand with BitLocker. Secure Boot ensures that the operating system and firmware are genuine and have not been tampered with, creating a secure foundation for BitLocker encryption.
- BitLocker in Enterprise Scenarios: Key Management and Recovery Planning
In large-scale enterprise scenarios, effective key management and recovery planning are critical aspects of BitLocker implementation. Administrators must establish robust key management practices and recovery procedures to maintain data accessibility while upholding security standards.
- BitLocker in Multiboot Environments: Navigating Complexities
Users employing multiboot configurations with multiple operating systems on a single device should be mindful of BitLocker’s compatibility with such setups. BitLocker is compatible with multiboot environments, but users must take specific steps to ensure proper encryption across all operating systems.
Future Considerations and Technological Advancements
As technology evolves and security threats become more sophisticated, Microsoft continues to refine and enhance BitLocker. Users can anticipate ongoing improvements, additional features, and enhanced compatibility with emerging technologies. Staying informed about updates and exploring evolving functionalities will empower users to continually optimize their data security strategies.
Conclusion
Windows 10 BitLocker Encryption stands as a stalwart guardian in the realm of digital security, providing users with a robust and comprehensive solution for protecting their data. By understanding its fundamental principles, implementing best practices, and exploring customization options, users can harness the full potential of BitLocker to create a secure digital environment. Whether safeguarding personal files, protecting corporate data in enterprise settings, or ensuring the confidentiality of sensitive information, BitLocker Encryption emerges as an essential tool in the modern era of data security.